Secure file sharing with anyone
FileSharing Business
Take control of your file sharing, file requests, emails, and attachments
/ user / month, billed annually
- Starts from 3 users
- Security control (expiration, password, disable download, email notifications)
- Encrypt emails and replies
Tresorit named a 2022 Gartner® Peer Insights™ Customers' Choice for Content Collaboration Tools. See the key insights for IT decision makers!
Read the full report
Every unencrypted file that is shared is a vulnerability
In traditional file sharing processes, files aren’t encrypted earlier on the client but only on the server as it is more convenient to view, manage, and index unencrypted files.
And even if the files are encrypted, the files and their keys are stored in the same environment. If the environment gets compromised, it won’t be long before keys are discovered and your sensitive data gets violated. Leading to irrevocable data detriments, financial loss, and even defamation.
Staying compliant while sharing sensitive documents shouldn’t be so hard.
Encrypt and control access to all files no matter where or how they’re shared
With a 5-step E2E encryption and zero-knowledge ciphering system, Tresorit’s FileSharing system transfers your files in unbreachable, fully encrypted data vaults.
So you can grow your business confidently while staying compliant – effortlessly.
12000+
Businesses around the world trust Tresorit
12 years
of excellence in serving our clients
0
breach incidents reported since 2011
Secure your company’s file sharing processes now
No need for cloud storage. Tresorit lets you share files securely and confidently with end-to-end encrypted email and secure file transfer.
Easy end-to-end encrypted file sharing
- Secure how teams and users share sensitive files even in cloud environments through zero-knowledge link sharing.
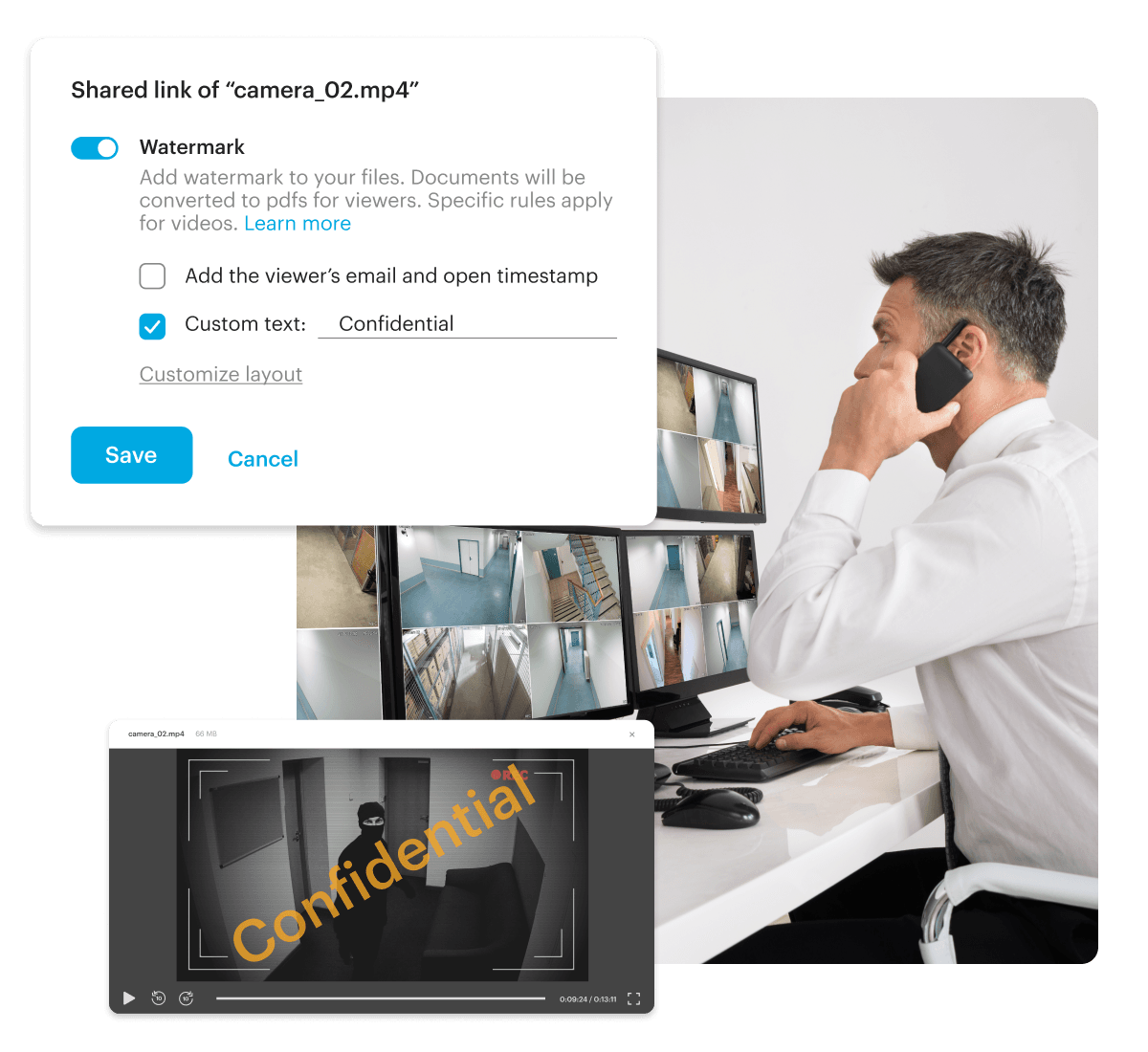
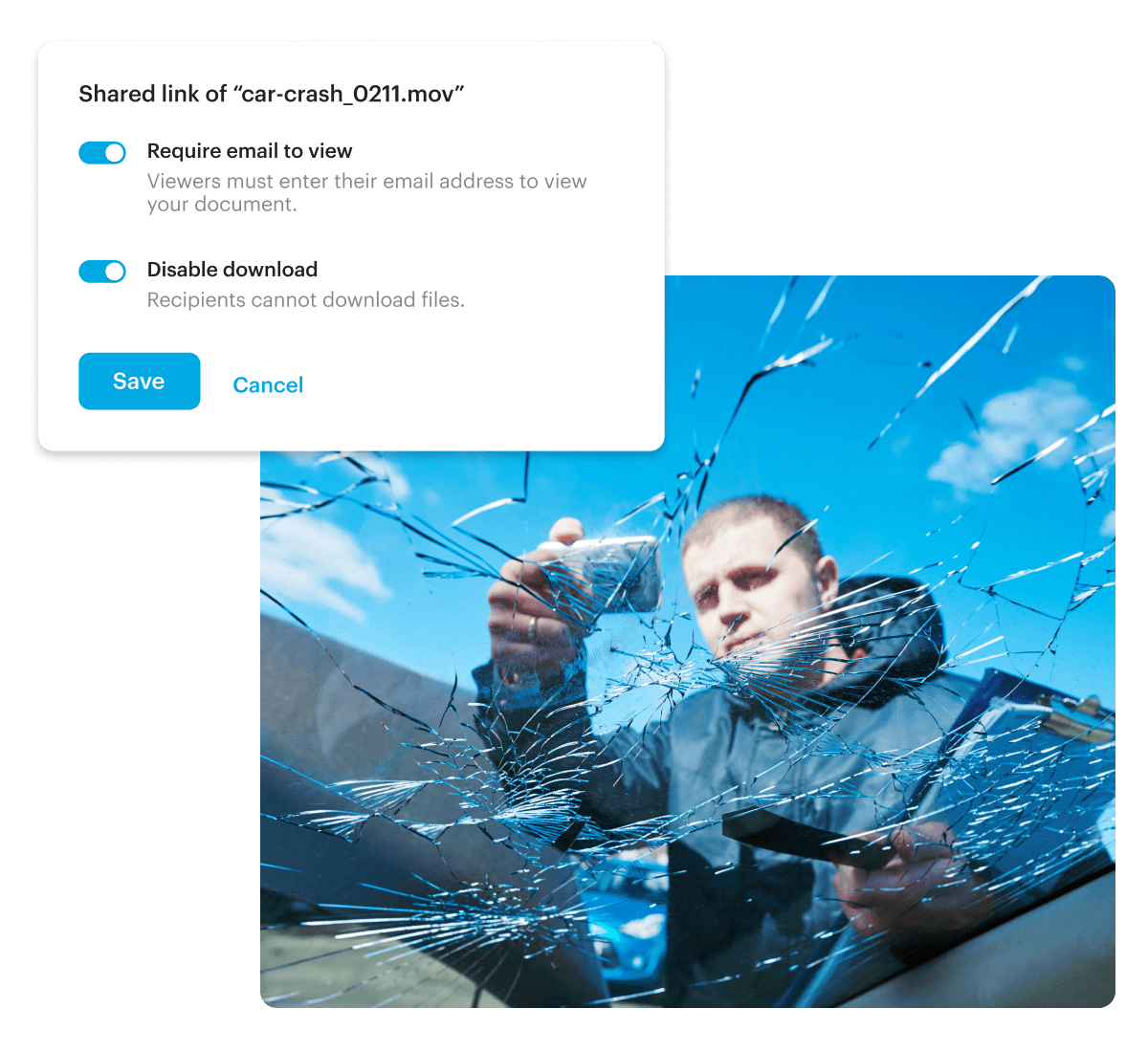
- Apply granular safety controls such as Allow list, Open limit, Disable download, Watermarking, and Automatic expiry deletion to potential data breaches.
- Share large, encrypted files simply and quickly with internal colleagues and external partners under the guidance of admin controls and email policies.
- Stay in line with business compliance by generating auditable Access logs, SIEM integration and activity reports in just a few clicks.
See How Different Industries Use Tresorit To Share Digital Evidence
Eliminate the risk of data loss with Tresorit FileSharing
Add multiple layers of security to confidential files to stay compliant and protect your company’s precious data. No matter where, when, or how your company shares files.
FileSharing Business
Take control of your file sharing, file requests, emails, and attachments
/ user / month, billed annually
- Starts from 3 users
Key features
- Security control (expiration, password, disable download, email notifications)
- Encrypt emails and replies
FileSharing Enterprise
Scale your business and receive volume discount pricing
Tailored for your requirements
- Starts from 50 users
Everything Filesharing Business, plus
- Multiple data residency options
- Custom GDPR DPA
- Integrations included (such as AzureAD, Okta, Sentinel)
Master secure file sharing with our comprehensive ebook:

- Discover how to safeguard your sensitive data, implement robust encryption techniques, and fortify your defenses against cyber threats.
- Gain valuable insights to ensure the privacy and integrity of your shared files.
Need a packaged solution with a secured cloud storage?
Find Tresorit FileSharing fully integrated in Tresorit SecureCloud
Trusted by 30,000+ customers worldwide
Resources
Frequently asked questions
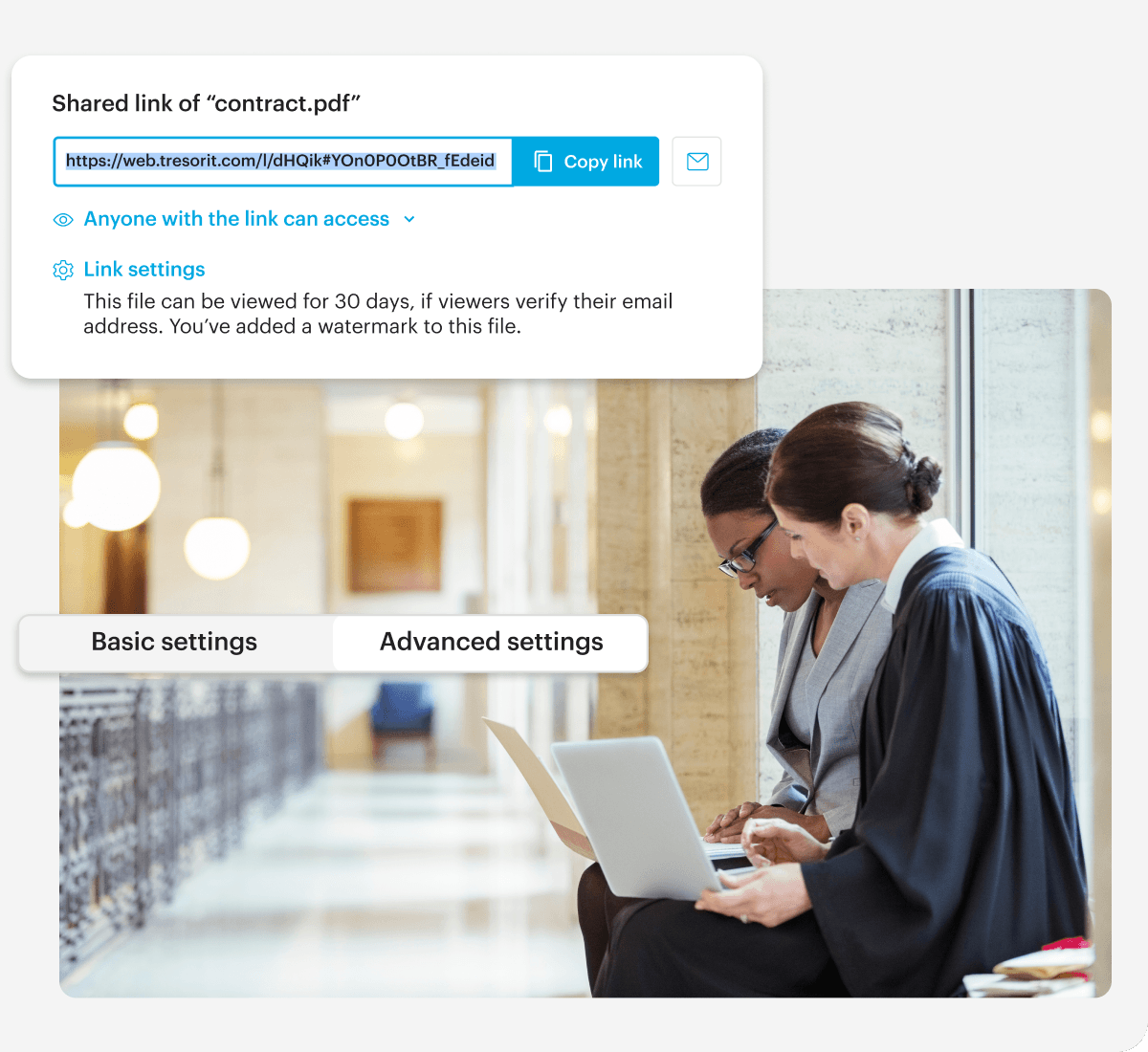
- Learn more about Tresorit’s securityEnd-to-end-encrypted file transfer is the most secure way to exchange files and documents.Using client-side end-to-end encryption coupled with zero-knowledge authentication, Tresorit encrypts every file and relevant metadata on your devices with unique, randomly generated encryption keys. These keys are never sent to our servers unencrypted. This means only data owners and any intended recipients can access the data stored in Tresorit, allowing you to share files with trusted recipients in full confidence.
- Learn more about our sharing optionsWe’ve designed Tresorit with a simple fact in mind: People don’t use complex security features that get in the way of getting things done. That’s why Tresorit provides you with different options to share your data in a convenient and secure manner.Sharing via secure links, collaborating in folders or sending encrypted attachments right from your email client – thanks to the various ways of sharing, Tresorit is always at your fingertips to help you protect valuable data.
- Learn more about Tresorit’s control features for shared filesDifferent file sharing methods and security features ensure you retain maximum control over your data.You have the option to define recipients by requiring email verification, adding passwords, or restricting access to allowed users specified at the email address or domain level. Access logs can be used to monitor who has opened the shared file, when, and on what kind of device. Additional features such as adding watermarks and disabling downloads ensure greater file security.
- Learn more about file requestTresorit enables secure two-way file sharing between organizations and external parties using secure links and file requests.You can easily exchange files stored in Tresorit with collaborators who don’t have a Tresorit account. Send secure links via your Tresorit app, or our Outlook and Gmail add-ins. However, external collaboration often requires two-way communication and a secure way of collecting sensitive files from your external parties, such as contracts, tax documents, financial or personal data. In these cases, you can create end-to-end-encrypted file requests that allow external parties to upload files directly to your fully protected Tresorit workspace.
- Learn more about sharing policies and other admin controlsThe Tresorit Admin Center is a purpose-built tool to help admins stay on top of company file activities regardless of your organization’s size.Deployment to the workflows of large teams is supported by our integrations and features for workspace admins. SSO support, team-level and role-based security policies, and reports on user and file activities ensure your admins have all the data they need to ensure your files are being kept safe.
- Learn more about Tresorit’s securitySecurity and privacy are key principles of how we operate. Our zero-knowledge end-to-end encryption (e2ee) provides the highest level of security and privacy for sensitive company data. We comply with the strictest security standards and protect all data in line with Swiss privacy laws.All data stored in Tresorit is only accessible to you and your intended recipients. Tresorit’s client-side encryption means that we cannot decrypt your files to hand them over to law enforcement because we don’t hold the encryption keys, or your passwords.Tresorit handles data according to Swiss privacy laws that guarantee one of the highest standards of data protection worldwide. By offering data residency options in various countries, we allow companies to decide where they want to store their data. Tresorit is ISO-certified and provides compliance with various local and industry regulations, including GDPR, CCPA, HIPAA, FINRA, and TISAX.