Launching “Link settings policy”
We are delighted to announce a new control feature to further increase admin control over company data. We have launched the “Links settings policy” with which admins can further customize user group policies.
The challenge of safeguarding company data
Cloud services have opened up new horizons in collaboration. But they have also brought new challenges in the form of accidental data leaks and hacker attacks. In the last couple of years, businesses of all sizes and industries have become increasingly popular targets for cyber-attacks. Cyber-criminals infiltrate through the weakest link, which often happens to be the company’s workforce. Almost 12% of breaches are due to human error, and most of them could be prevented with well-defined security measures. However, it’s easier said than done, and only 38% of global organizations claim they are prepared to handle more sophisticated cyber-attacks. The thing is, as long as businesses are connected to the internet, they have a good chance of becoming a victim. At the same time, they cannot afford to lose the benefits of cloud solutions. Giving up the quick and easy implementation, the savings on IT costs and accessibility would hurt productivity and competitiveness too much. In order to stay safe in the cloud, businesses need to put company-wide security policies into effect to prevent data loss.
Controlled content sharing
We are very proud to provide the most advanced secure file sharing method on the market. With Tresorit you can replace risky email attachments with bulletproof, end-to-end encrypted links. Using links instead of attachments is easy. All you need to do is select the files you wish to send, create a link and share it via email, chat or whatever you prefer. Recipients can download the files from a download page by simply clicking on the link.
On top of end-to-end encryption, we provide granular settings to further improve security. Senders can setup the following:
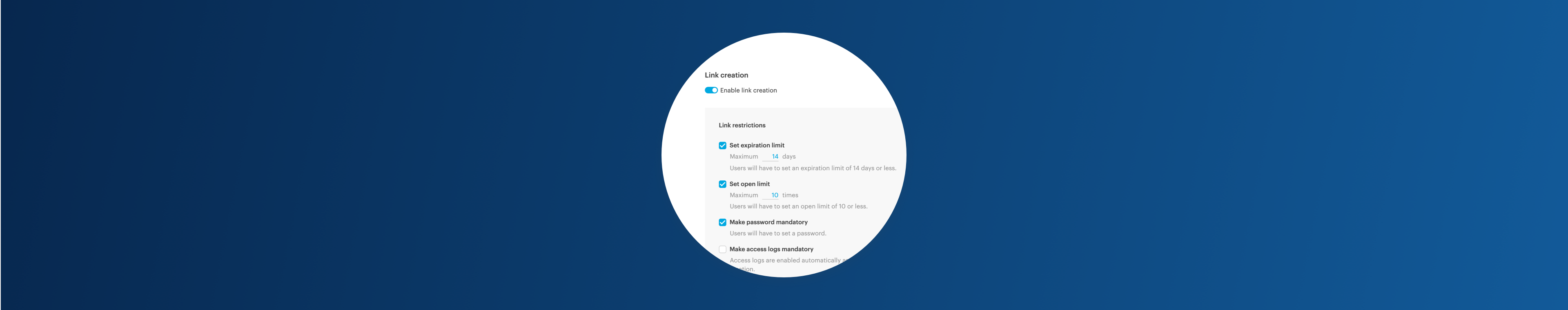
- Expiration date: Set an expiration date for a Share Link if you don’t want your recipients to access the shared content after a certain date.
- Open limit: Set an open limit, after which the Share Link automatically becomes inaccessible. From that point on, nobody can retrieve the shared content from the download page.
- Password protection: Add passwords to your links to improve security further. When recipients open the link, they will need to enter the password you created.
- Require email verification: Make email verification mandatory for opening a shared file. When email verification is on, recipients are asked on the download page to provide their email address.
- Access logs: You can enable Access Logs for each Share Link to see the open date, email, IP address and platform used to open the links you shared.
Confident control over company data
With the all new “Links settings policy” you can prevent accidental data leaks. This new feature further improves the security of file sharing. Admins can set up different link share policies for selected user groups. Password protection, access logs and email verification can be made mandatory and the expiration date and open limit can be maximized.
When to use
Link settings policy can help any kind of organization which wants to make file sharing even more secure for a selected group of users.
Take this scenario for example. A group of users in a company frequently shares confidential offers with clients. In this case, admins should maximize the expiration date so offers won’t be accessible after they expire. They should make access logs and email verification mandatory, so the company will always know who opened the offer, and when.






