TISAX: From safety to security – Automotive industry doubles down on data protection

Tresorit supports companies in achieving TISAX certification
Traditionally, safety was the name of the game in the automotive industry. However, as safety is now increasingly powered by software – for automated driving or V2X communication – and digitization has transformed the world of work, security is becoming just as important. That’s why OEMs regularly request evidence of compliance with stringent information security requirements from their suppliers.
TISAX – The what, where and why
TISAX, or the Trusted Information Security Assessment Exchange, is a common security standard for the automotive industry to protect all data created during the development and production processes. Brought to life by the German Association of the Automotive Industry (VDA) in collaboration with the ENX Association, TISAX regulates Information Security, Data Protection, and Prototype Protection. Every company in the supply chain of the affected car manufacturers must comply with its guidelines anywhere in the world. Manufacturers and suppliers alike can benefit from this standardized certification process by reducing the cost and effort of multiple information security assessments.
What are the implications of not complying with TISAX guidelines?
TISAX is one of the automotive industry’s self-regulative initiatives. Only a few institutions are allowed to conduct TISAX certifications. The ENX Association is entrusted with the entire governance and platform operation of TISAX. Companies that achieve a Level 3 or higher on the standard’s maturity level scale are listed in the TISAX database, which is made accessible to members of the VDA and certified companies. There is no third-party regulatory body to enforce long-term compliance.
Despite this, lacking TISAX certification will bar companies from doing business with automotive OEMs and their suppliers. As more and more companies expect a high level of security from their suppliers, the pressure is growing throughout the automotive industry.
How to attain your TISAX labels?
TISAX is a standardized way of proving compliance with the VDA’s Information Security Assessment (ISA) catalogue and sharing this information with other participants. Companies generally are required to attest their TISAX compliance by a partner or chose to participate proactively. A TISAX assessment usually includes the following steps:
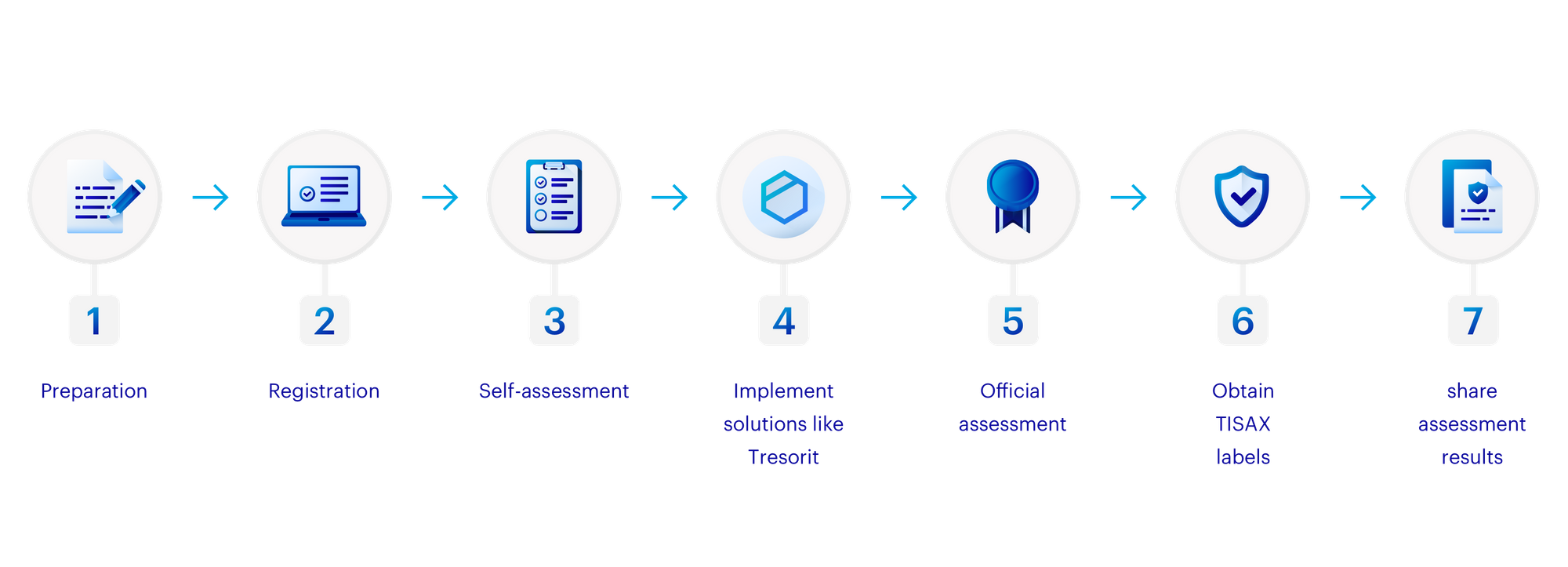
- Preparation: TISAX will require planning from every company – even for those who information security a priority. The journey begins with learning, and the TISAX Participant Handbook is the best place to start.
- Registration: The first step participants must take is registering on the ENX platform. The scope of TISAX audits are predetermined; assessment objectives must be selected during registration. As audits are location-specific, you may need to submit several registrations.
- Self-assessment – Use the VDA ISA catalogue to gauge whether your information security management system is ready for TISAX. As the official assessment process is limited to nine months, it is better to implement required changes beforehand, without time pressure.
- Implement solutions – Make changes to internal and external processes to ensure compliance with the Information Security section of the VDA ISA catalogue and any other chapters required by your scope. Deploy Tresorit to enable the end-to-end encrypted storage and secure sharing of your information internally and with partners. Tresorit can be deployed easily, regardless of how many locations your company operates in, and it secures data exchange across your international operation.
- Official assessment – Select an assessment provider and begin the official assessment process. Work starts with an initial assessment, during which issues to be addressed are identified. Steps are taken according to a corrective action plan once the selected provider has confirmed the plan itself. Finally, a follow-up assessment reviews changes and ensures compliance. With thorough preparation and implementation of the right IT security tool suite, this phase can be over quickly.
- Obtain TISAX labels – If the assessment is successful, the objectives defined in the registration process become labels that prove compliance for three years. Certain labels are hierarchically linked. For example, if a company is granted the label “info very high” it automatically receives “info high” as the latter is a subset of the former.
- Share compliance – TISAX compliance is shared on the ENX platform. As the entire audit process is conducted on the platform, setting up the sharing of your labels with other participants to prove compliance is straightforward.
How does Tresorit support compliance with TISAX?
TISAX lays out clear guidelines for communication and data transfer within the automotive industry. These require that companies ensure all data is encrypted for transport or transfer. However, to achieve higher maturity levels and fulfill requirements for very high protection needs, companies must ensure that all communication to and all data stored on externally hosted IT systems is secured with end-to-end encryption (E2EE). This can cause headaches when sharing data between company hubs and with external partners. Thankfully, Tresorit offers a host of functionalities that support companies in their journeys towards achieving TISAX-certification:
- Safe storage: Zero-knowledge E2EE storage offered by Tresorit ensures data remains secure at rest and in transit. All information is stored in several different storage centers to avoid data loss.
- Sharing attachments via secure links: Email attachments are insecure and not TISAX-compliant – especially when email traffic is not encrypted. Replace attachments with links from Tresorit to maintain compliance. By setting passwords, expiration dates and disabling downloads, employees retain full control over shared files.
- Easily integrate Tresorit into existing workflows based on Office 365: TISAX rules can cause significant disruption to well-oiled workflows. Tresorit brings these to a minimum with its outlook integration, allowing users to share files without leaving their email client and automatically transforming any attachments into secure, Tresorit share links.
- Administrative efficiency ensures minimal disruptions: Tresorit includes a set of Admin tools, including an Admin API and SSO integrations, to cause minimal disruption to the workflow of large enterprises. Role templates and the admin dashboard ensure admins are never stuck in endless administration tasks.
- Secure partner collaboration: E2EE file requests allow engineering teams to collect documents from external suppliers securely.
As data security becomes increasingly important to the automotive industry, there’s never been a better time to start your TISAX compliance journey. Find out more about Tresorit’s pricing plans here.






