NIS2 and secure cloud infrastructure
The NIS2 Directive strengthens cybersecurity and operational resilience requirements across the European Union. As digital infrastructure becomes a critical dependency for organizations, protecting sensitive information and ensuring service continuity are central to regulatory expectations.
Tresorit supports affected organizations with a security-first cloud platform designed to reduce data exposure and support structured risk management.

What NIS2 means in practice
NIS2 expands cybersecurity obligations for essential and important entities within the EU. It emphasizes structured risk management, protection of network and information systems, incident preparedness, and operational resilience.
The directive reflects a broader shift: cybersecurity is no longer solely a technical concern but a governance-level responsibility affecting business continuity and digital trust.
Who NIS2 applies to
NIS2 applies to organizations classified as essential or important entities, including operators in critical sectors and digital service providers.
Applicability depends on sector classification, organizational size, and role within critical supply chains. Organizations operating across EU member states may also be indirectly affected through contractual or risk management obligations.
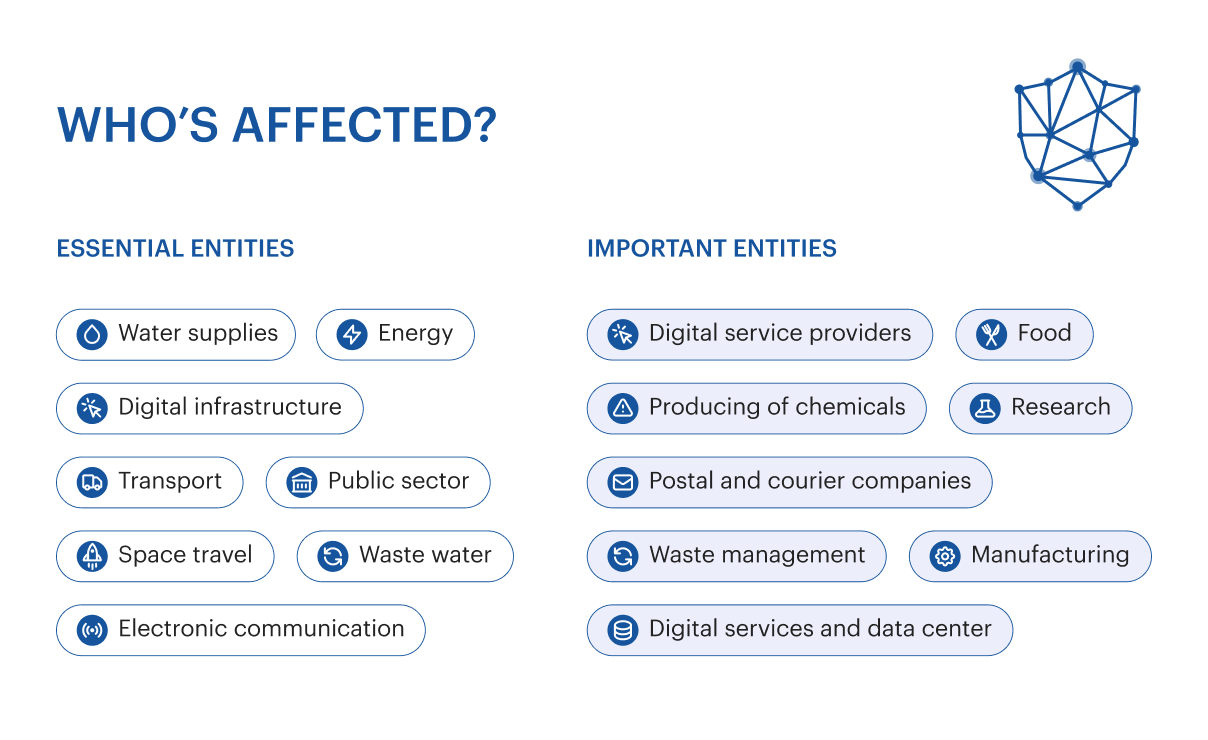
Who NIS2 applies to
NIS2 applies to organizations classified as essential or important entities, including operators in critical sectors and digital service providers.
Applicability depends on sector classification, organizational size, and role within critical supply chains. Organizations operating across EU member states may also be indirectly affected through contractual or risk management obligations.
Tresorit’s role in the NIS2 context
Under NIS2, organizations remain responsible for meeting regulatory obligations. Cloud service providers, however, form part of the broader digital risk landscape.
Tresorit supports organizations by limiting data exposure, strengthening access control, and providing secure collaboration infrastructure designed to reduce cybersecurity risk in distributed environments.
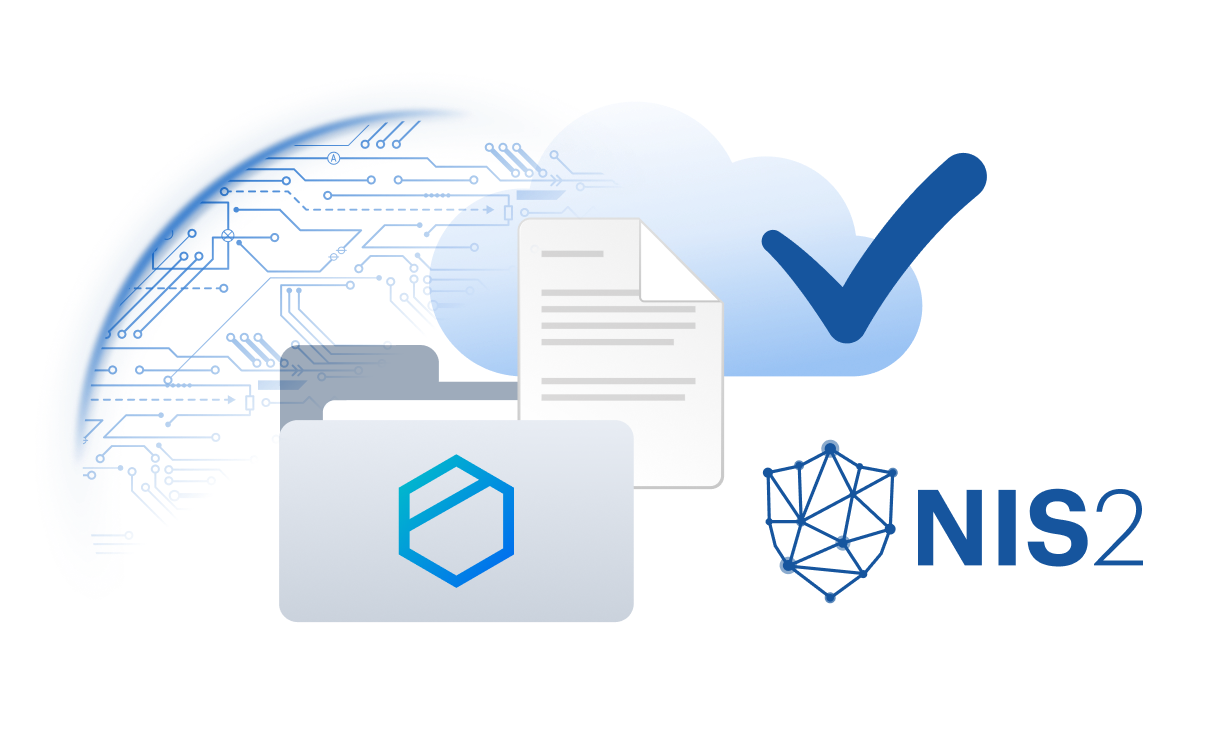
Security architecture and resilience
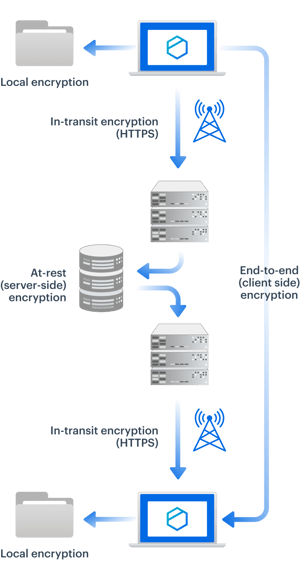
Tresorit’s architecture is designed to minimize unauthorized access and reduce systemic risk. Client-side encryption ensures that sensitive information remains protected before it leaves the user’s device.
Combined with strict access controls and controlled sharing mechanisms, this architecture supports organizational resilience in environments where data exposure is a key regulatory concern.
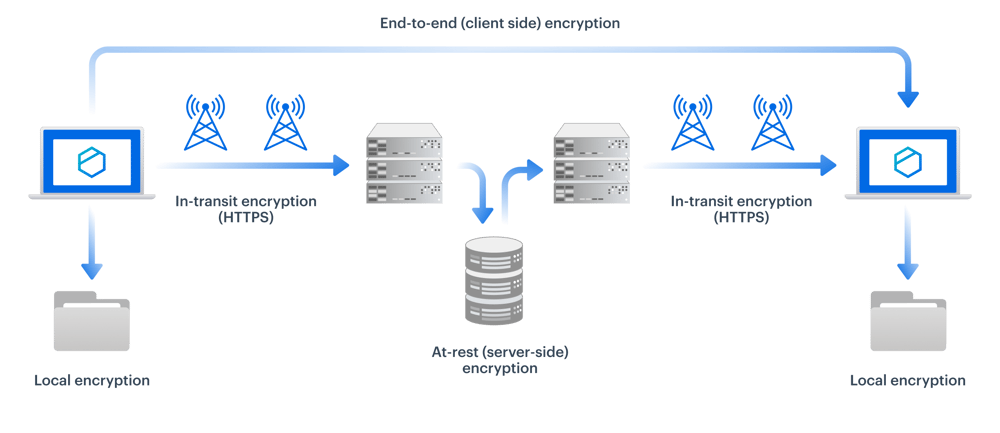
Security architecture and resilience
Tresorit’s architecture is designed to minimize unauthorized access and reduce systemic risk. Client-side encryption ensures that sensitive information remains protected before it leaves the user’s device.
Combined with strict access controls and controlled sharing mechanisms, this architecture supports organizational resilience in environments where data exposure is a key regulatory concern.
Incident response and operational continuity
NIS2 emphasizes timely incident detection and response. While compliance obligations remain with organizations, the resilience of underlying service providers plays a critical role in maintaining operational continuity.
Tresorit operates monitored systems and maintains structured security practices designed to support reliability, transparency, and responsible incident handling.
How Tresorit supports NIS2 requirements
Fortify your supply chain’s security posture — NIS2 article 21, (2)h
Encrypt vulnerability disclosure channels — NIS2 article 21 (2)e
Bolster your incident handling processes — NIS2 article 21, (2)b
Effortlessly empower cyber hygiene practices — NIS2 article 21, (2)g
Ensure business continuity via a resilient platform — NIS2 article 21, (2)c
Automate & enforce strong access control policies — NIS2 article 21,(2)i
Secure collaboration with automatic encryption — NIS2 article 21, (2)h
Secure system acquisition & development — NIS2 article 21, (2)e
Customer Success Stories
NIS2 FAQ
NIS2 applies to organizations, not products. Tresorit supports customers with security and data protection measures aligned with NIS2 requirements.
No. Compliance depends on organizational measures. Tresorit provides supporting technology and security foundations.
- Risk analysis & information system security
- Incident handling
- Business continuity measures
- Supply chain security
- Security in system acquisition, development & maintenance
- Policies and procedure to assess the effectiveness of cybersecurity risk management measures
- Basic cyber hygiene practices and cybersecurity training
- Policies and procedures on the use of cryptography and encryption
- Human resources security, access control policies and asset management
- Use of multi-factor authentication, secured voice/video/text communication and secured emergency communication
- For essential entities: administrative fines of up to 10 million euros or 2% of the total annual global revenue in the previous fiscal year, whichever amount is higher.
- For important entities: administrative fines of up to €7 million or 1.4% of the total annual global turnover in the previous fiscal year, whichever is higher.

NIS2 compliance through security by design
NIS2 reflects a broader European focus on cybersecurity resilience and digital risk management. Tresorit supports affected organizations with secure cloud storage and collaboration infrastructure designed to protect sensitive information and contribute to structured risk mitigation efforts.
For detailed compliance assessment, organizations should consult legal and regulatory advisors.
Essential resources to NIS2 compliance




