Tresorit vs. Nextcloud: Why choose Tresorit?
Trusted by 11,000+ organizations worldwide
On-premises-level security for your data in the cloud
Tresorit brings the highest levels of security and control – benefits primarily associated with self-hosted solutions – to the cloud. Powered by our innovative zero-knowledge end-to-end encryption, our content management, and collaboration tools allow you to share, manage and control sensitive files in the cloud. By creating a fully encrypted environment for your internal and external collaboration, our solution makes any third-party access to your data technically impossible.
We believe that ease of use paves the way for secure user habits. That's why we have designed our solution to combine the most sought-after benefits of the cloud – security, and convenience – without the need for extra servers, resources, or hidden costs.
- PriceFrom /user/month – starting from 3 users€36/user/year – starting from 100 users
- Monthly offer
- End-to-end encryption by default
- Secure file sharingLimited
- External file exchangeLimited
- Outlook and Gmail integrationOutlook only
- Admin controls and monitoring toolsLimited
- Real-time collaborationNot possible with true E2EEOnly when E2EE not enabled
- Email encryption
Need a compliant solution for storing and sharing files?
Security and compliance by design
External file exchange with peace of mind
Easy deployment, management, and control – centrally
Unlock the convenience of cloud collaboration, without compromising security

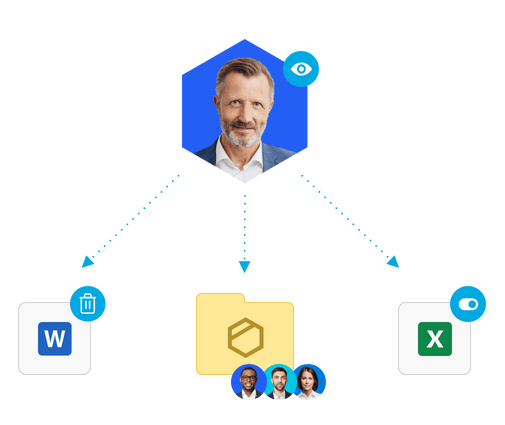
Manage and control your valuable content in the cloud
End-to-end encryption is integrated into our product. This means that everything you do in your Tresorit Secure Cloud will be seamlessly secured from the ground up - without the need for separate add-ons and any interruption to your work.
To increase team productivity and nurture external collaboration, you can firm up your security with specifically designed controls - both on a user and admin level.
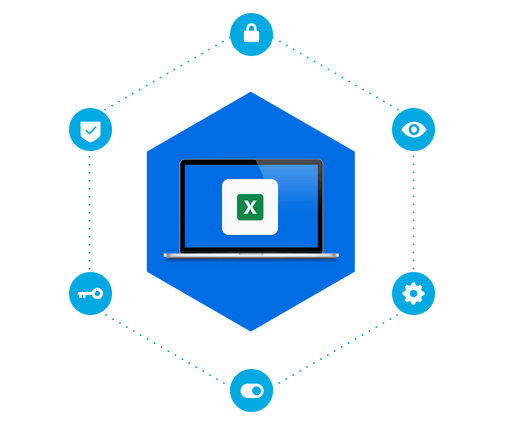
Security & compliance
With Tresorit, end-to-end encryption is available from your very first sign-in and always at work whenever you use our tools. Thanks to our client-side encryption, no third-party provider - not even Tresorit - can access your encryption keys and read or scan your files. Thus, compliance with the strictest data regulations is not dependent on extra installation or human diligence but inherently assured through our technology. For greater control over your data, you can choose from our data residency options available in 12 regions.
Nextcloud employs transfer encryption by default. In addition, server-side encryption can also be enabled by admins. However, with keys stored on the Nextcloud servers, this doesn't prevent admins or malicious intruders from accessing the users' files. Nextcloud offers end-to-end encryption as an extra feature only for folder sharing. As e2ee is only available as an add-on, there is room for security flaws and human error, which ultimately puts your security and compliance at risk.
File sharing
Tresorit makes file sharing possible anytime and anywhere by using ultra-secure links. With Tresorit's plugins for Outlook and Gmail, even your usual preferred communication channels are protected in the best way possible. For external collaboration we provide an unprecedented choice of security controls, including advanced link tracking, watermark, allowed users, and document analytics.
File exchange with Nextcloud is not end-to-end encrypted by default. E2ee can only be enabled for sharing folders/subfolders, making the exchange of sensitive files a cumbersome process. Nextcloud offers limited security settings for share links: only expiration date, password protection, and user permissions are available. Therefore, it cannot prevent threats resulting from unauthorized document download, editing, or reuse.
Collaboration
Real-time collaboration is contrary to the way end-to-end encryption works. While collaborative editing with Tresorit has its limits, you can avoid creating version conflicts by marking files as editing. In addition, you can empower teamwork with features such as Tresorit paths, synced project folders, access permissions, integrations, and more.
Nextcloud excels in offering integrations with document collaboration tools - such as Collabora or ONLYOFFICE - and capabilities for online meetings and conferencing. Real-time collaboration, however, comes with the trade-off of allowing scanning and analyzing of your file content – and can thus compromise your data security.


