Privacy Checklist - Beyond EU Data Protection Policy (GDPR)

Tresorit founder and top cryptography expert, Istvan Lam, welcomes the new EU Data Protection Policy (GDPR), despite the strong belief that a single regulation is not enough to ensure privacy for European internet users. As this is a very complex matter, he suggests an easy-to-use checklist to help you identify online services that are designed to go beyond EU Data Protection Policy and maximize your data protection.
Today, the European Parliament made the final vote on the new EU Data Protection Policy, also known as GDPR. It is going to enhance and unify data protection and privacy for European internet users by the year 2018.
However, there’s still a long road ahead of us. If we compare this change to the security standards of the automotive industry, it means that internet users are now going to get their default seatbelt, but other important security measures such as ABS and airbags, are still not available.
.
The new EU Data Protection Policy is not a ‘magic pill’ for our online privacy problems. For example, GDPR still leaves room for government authorities to conduct mass surveillance through backdoors. Despite having the best intentions and expertise of lawmakers, this regulation by itself will never be enough to guarantee data privacy online.
Checklist for the 3 levels of data security & privacy
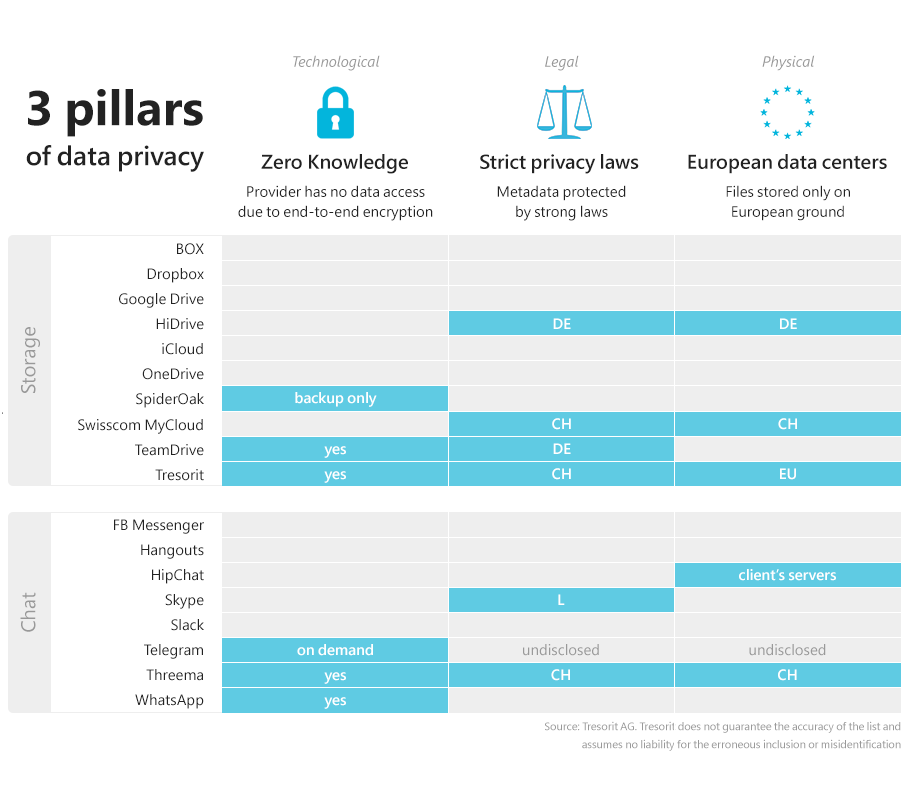
There are 3 main pillars of data security: technological, legal and physical. The safest solution remains a combination of end-to-end encryption by trustworthy European providers with European servers. That way you can be sure that the whole service is designed to ensure your privacy (“Privacy by Design”). There are great examples of companies meeting these standards, such as the email service ProtonMail or the messenger app Threema. And just like them, Tresorit also addresses security and privacy on all three levels.
Checking the items off of this list can be beneficial to everyone when picking a secure provider without having to dig too deep into the small print and technical details of each service. Doing so can also be helpful, for example, when trying to understand why WhatsApp’s new end-to-end encryption still doesn’t give you complete control over your data.
- Technological: Your provider should use “zero-knowledge” or “end-to-end encryption“. This means that your data is encrypted in a way that only your device can decrypt it. No government, hacker or provider employee is able to look into your files.
- Legal: Your metadata (the data your provider must have access to, such as your email address, credit card or location logs) should be protected by strict privacy laws. Some countries such as Germany, New Zealand, Iceland, and Switzerland are considered to provide such strong end user protection. Find out where your provider has registered their business on their “About us” or “Contact” page. Tresorit, for example operates under Swiss privacy law. That way, our customers’ metadata enjoy high protection and are also out of reach for any requests from US authorities.
- Physical: The location of your provider’s servers also has an impact on who can access your data and how well your files are protected against physical attacks. This is especially risky if the other two criteria aren’t met. Tresorit runs on Microsoft Azure with servers in the Netherlands and Ireland. We chose this service because it meets the highest physical security standards so that we don’t have to fear server outages and lost data (e.g. by earthquakes) and it also is certified to comply with high EU requirements.
On top of the 3 main pillars, we recommend to look for clues that show that the provider committed to protecting users’ data privacy: Are they making an effort to be transparent? Do they ask you to let them share your data with 3rd parties? If they ask for your personal details, do they tell you what they will do with it? The correct answer to these questions is a more subjective matter, but never stop paying attention and always ask yourself if you are really convinced by the explanations they provide.






