Why email providers must focus on security as much as banks
An op-ed from Arne Möhle, co-founder and CEO of the secure email service Tutanota.
Banks store people’s assets in the form of virtual numbers on their servers. Obviously, any bank must take utmost care that no one can hack into the servers and change the numbers. Email providers must do exactly the same. Because the email address is the link to your identity – and to all your assets stored online.
Unfortunately, not all email services understand today’s requirements for secure emails. This is, in parts, not their fault: When email set out to become a mass communication tool online, it was just that. A communication tool. But then the Internet evolved, many new online services were created, and they needed to identify their users.
By then, almost everybody using the Internet had an email address. In the beginning, people mostly chose their real name as an email address. So, to other online services it made absolute sense to enable people to sign up with their email address.
This is when people’s email addresses became much more than just a tool to communicate online.
Identities linked to email address
Once you use your email address to register with other services, the email address becomes the link to your online (and oftentimes offline) identity.
Amazon, Facebook, PayPal, Twitter – all of these services let you register with your email address. Once you’ve added your bank account or credit card to these online services, you can shop online, quickly and easily, and everything is handled via email.
This is all very good, except when it comes to security. All of these services offer a password reset via email. This means, whoever gets access to your email account, gets access to all your other online accounts – and can use your payment details to keep shopping online.
That’s the risk everyone of us is taking when registering with Amazon, PayPal and Co with an email address.
Hacks must be prevented by all means
Established email services from the early days of the Internet have not always kept up with security demands. Some do not offer second factor authentication (a must when you want to keep your email account secure!), some like GMX and Web.de let people sign up with choosing ‘password’ as a password.
This puts the trusting user at risk. When a service lets you sign up with an insecure password, and doesn’t offer second-factor authentication, it becomes impossible for the user to adequately secure their email account.
The solution can’t be to say, people should educate themselves, should learn everything there is about password security and so on. While of course, this is also important, the biggest responsibility lies with the email provider.
Email providers must take on responsibility
If a hacker gains access to your bank account, the bank usually replaces any loss – it’s called reputation management. If a hacker gains access to your email account, then takes over your PayPal account via a simple password reset – who will replace your loss?
In this scenario, the email provider and PayPal are to blame. If the email provider allowed you to sign up with a weak password or did not adequately protect against brute-force attacks or did not store your password encrypted on the server and suffered a breach – then obviously the fault lies with the email provider.
At the same time PayPal is to blame: A password reset via email is simply too easy to abuse and, in consequence, should not be offered.
Necessary steps to keep online identities secure
Every online service must review their password guidelines to offer best password protection possible. Obviously, this includes not allowing ‘password’ as a legit option for setting a password. It also includes adequately protecting against brute-force attacks, hashing/encrypting stored passwords, and enabling to sign up with long passwords, including all uni-code characters.
In addition, every email provider must offer two-factor authentication and educate its users about email security.
Call for strong focus on security
But while all this is fine and dandy, it is by far not enough.
Online services in general must focus on security. As illegitimate account take-overs such as the ones of Mat Honan and Naoki Hiroshima have shown, it is even possible to hack a high profile target by being a very convincing attacker who is able to persuade tech support that they were the rightful owners of the targeted online accounts.
Attacks like these show that the weakest point in online security is your password.
Password resets are problematic
Allowing people to simply ask for a password reset via email makes it very easy for potential attackers to take over these accounts – because once they have your email, they have everything.
That’s why password resets via email are so problematic. We need much stricter requirements for password resets to make sure there is no room for abuse. Tutanota, for instance, gives people a recovery code, which they can use to reset their passwords.
The beauty in this is: We as the provider have absolutely no access to users’ passwords. Even if we wanted to, we couldn’t hack our own users. That’s why the users need to write down their recovery code.
And while this system is not perfect – because, unfortunately, there will always be people, who manage to forget their password and their recovery code – it is secure.
So what should the users do?
As a rule of thump, activating 2FA on every online account is always a good idea. Choosing a secure email service comes next.
The way most online services work – and it’s unlikely that this will change in the near future – is that they offer password resets via email by default. Sometimes you can disable this option, most of the times you can’t.
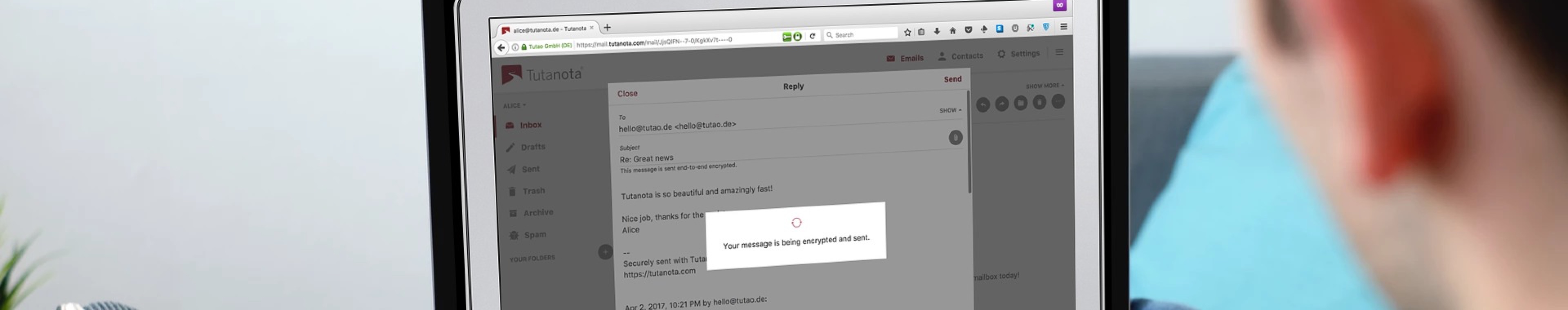
This means, you must make sure that no one, under no circumstances whatsoever, is able to gain access to your email account. As Tutanota focuses on security by encrypting your entire mailbox automatically, it naturally also puts a high priority on best possible password protection.
Here are some password security measures that Tutanota has built into its code: only strong passwords are allowed, the passwords are hashed on the client as well as before storing them on the servers, uses state-of-the-art brute-force protection, offers two-factor authentication, a password reset is only possible with the recovery code, and has encrypted storage of data.
However, no matter how well a service secures the login credentials, the users have to make sure that no one can guess or phish their passwords. That’s why it is of utmost importance that you never fall for email phishing attacks.
Thanks for reading, stay secure.
 |
About Arne Möhle:
Arne Möhle is one of the founders of Tutanota and develops the secure email clients for businesses and individuals. He writes code to end mass surveillance and industry espionage – by automatically encrypting all emails. |






